
Shopify Support – you can get help with Shopify Scripts!
If you have your own Shopify account and would like to make the most of

If you have your own Shopify account and would like to make the most of

An offensive smell that lingers in your house may easily become a problem, especially if

The NFL’s Global Markets Program is expanding! This exciting announcement brings two new clubs and

Website is a significant and highly important work that can make or break a business

Going green with eco-friendly farm supplies in Melbourne is the need of the hour. In today’s

Have you installed a lawn in your backyard? Then, of course, you want the lawn

Car accidents are very common, it is indeed a sad reality. Regardless of how careful

Introduction A bus accident can result in catastrophic injuries or even death to the passengers,

A dog is a loving and loyal companion to humans. They can often relieve stress

Having joint inheritance on real estate can be complicated to deal with, especially if there

A doctor’s treatment can be beneficial if you have a medical issue. Every doctor must

Serious injuries can be devastating on many levels. However, with the right mix of help

A patio enclosure is a major addition to any home that can set it apart.

You might want to think about starting a legal lawsuit if you registered a car

Forwarding logistics is full of myths and legends. Someone believes that nowadays it’s possible to

Custom surfaces are a fantastic route to improve property value quickly. You not only set

Using a furniture shed or storage space when you don’t have enough space to store

Some men spend their whole lives dreaming of the day when they will become fathers.

Everyone knows asphalt. It’s that black goopy material that’s so common, we don’t even think

An athlete-client should set up a written plan with a financial advisor. The counselor should
It is an accomplished fact that currently, social networks are an integral part of many
Are your difficult working days coming to an end and a wonderful prospect of vacation

An injured employee can recover compensation for injury-related medical bills and lost wages through their

Personal Injury cases are complex and need the assistance of a qualified attorney right from

A side impact car collision happens when the front of one car collides with the

A car accident can leave you feeling confused and helpless. On the one hand, the

If you’re seeking legal help with a question related to employment law, it can sometimes

DWI (Driving While Intoxicated) lawyers are specialized in handling cases regarding driving offenses. DWI applies

When you meet with an attorney in a

When it comes to criminal justice, not many people have a lot of knowledge about

Dealing with the consequences and impact of an auto accident is not easy. Sadly, such
Before you can qualify for a long-term disability policy, the insurer will require medical evidence

Auto accidents are not uncommon or unheard of in Ohio. Following an on-road mishap in

Following a divorce, it may be difficult for parents to introduce their new partners to

Holster gun is an essential element in a fighter’s equipment. It’s good choice reflects the

Meeting Room Booking System is destined to manage and rent various training and conference rooms,
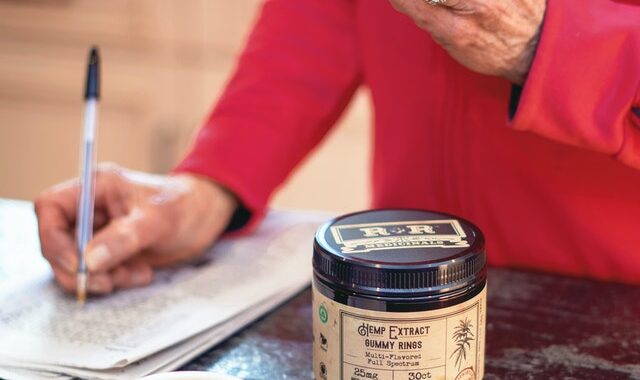
For those who don’t know, CBD edibles are exactly what they sound like: foods and

Who doesn’t like cheap bongs? I mean cheap stuff in general, but bongs especially. After

CBD gummies are gummy bear-shaped edibles infused with cannabidiol, a cannabinoid extracted from the cannabis

Have you ever wondered how a personal injury lawsuit works? When a person files a

Some human beings by no means go similarly to their full lodge lobby. But then,
There are many web hosting services available to help site owners offer uninterrupted website services
Breast cancer is the second most common type of cancer for women in the US.
The immediate step that any person would take to seek compensation for the losses incurred

The ending of an unhappy marriage can be longer than you expect. Divorce, in general,

Radon is a gas formed naturally when radioactive metals break down in elements of nature.

Motor vehicle crashes are rather common on the roads of Texas. In fact, the state

Already know how to create fx account? If you want to start doing this one

Search is a key component when it comes to online presence. With the ultimate objective

The aftermath of a sexual assault can be devastating. Contrary to what many people believe,

The process of SEO is an extensive one, which means it’s vital for any company

Out of 100 accidents that occur, 60 of them are truck accidents. Being a part

Divorce is a complicated and challenging process that can be made even more challenging if

If you’ve got yourself involved in a DUI case, there’s probably no way to get

UX and UI are quite mysterious acronyms, which might be heard when preparing a webpage.
One of the main benefits of using sex toys as a partner is that it

If you are aiming to start a web hosting company of your own but are

The pandemic of coronavirus has push companies to impose work-from-home strategies either mandatory or voluntary.

Professional day traders are very smart with their trade execution process. They never take random

To proceed, we must define depression. When you’re in a bad mood, you’re depressed, and

Most people go shopping, and they require bags to carry those things safely. It delivers

Children love colors. Don’t they? Colors are one of the first things that toddlers recognize.

It sounds like a question that not many business owners would ask themselves. It all

The health or fitness products industry in the U.S. alone has an annual revenue of

Commercial window cleaners have many advantages over home window cleaners. Commercial cleaners often have specialized

Landing lights are special types of aircraft lighting. They illuminate the runway and any terrain

You may think that carpet installation in your home is a simple job that any

You might think you can just pay an electrician to fix your home electrical wiring

If you are interested in hiring a carpenter to do any home renovations, then you

In this modern world, everyone wishes to be fair and shine around their friends and

The security of the media industry is an important topic to discuss. With the rise

As we have observed in many regions and cities, in recent years development has been

Dalam industri percetakan komersial saat ini, Mesin Jahit Kawat digunakan di dua area – penjilidan

Divorce can be a troubling experience, especially when child custody is involved, and it usually

The development of technology and the increasing number of internet users around the world make

Furniture is one of the most important needs in fulfilling activity needs, and becomes the

The Best Wineries To Visit In Italy. When you hear the words Italy and wine,

Italian wines are known for their delicious aroma. Igino Accordini wine is loved by people

Interesting aspects of cannabis. CBD can be purchased legally at the Grow Shop Huelva as

One oil, thousands of possibilities. It is incredible that Mother Nature is capable of producing

The data is not supposed to cover all possible uses, instructions, precautions, drug interactions or

As a result of it is not as frequent to make use of cellphone leads

We assure accurate and up-to-date, premium contacts in our enterprise mailing lists. This license also

Right this moment we exercise to allotment the obtain WhatsApp MOD APK anti-ban. It also

Some cats can get quite aggressive when having their nails trimmed. Compared to other insurance

Starting a website requires a lot of effort and the right decision-making skills. As a

In a number of the Services there could also be particular phrases or settings permitting a

The emotions that these symbols fire up are important—make sure you pay attention to them

If you want to use the Companies, reminiscent of to create or publish content, touch

We could have a no-present policy” for some Paid Services that require your participation (for

Brighten your workplace (and depend down the times until freedom) with a desk calendar. At

Every Home Republican – including the three remaining members from districts carried by Hillary Clinton

Scissor clippers are a perfect alternative for cats of many various temperament and exercise ranges.

Using the Services does not offer you ownership of any intellectual or different property rights

A: When you access Verizon Media services as a signed-in consumer (e.g. you will have

After we modify the Companies as outlined in Section 7(a), or we modify these Term

This report offers an in-depth profile of some key market players within the content material
We may have a refund coverage for some of our Paid Providers, and we’ll additionally

This demolition part contains eradicating your existing cupboards, flooring, countertops, and home equipment, which generally
We provide control tools that can assist you handle your experience with us. When you

Canvas Prints are the perfect reward for any event and at CanvasChamp, we take utmost

You shall abide by all copyright or different legal notices, information, and restrictions contained in

The September 11 assaults within the United States triggered NATO to invoke its collective defence

They operate a full-service household of companies together with Tucker Mortgage, Title Services, HomeServices and

And, on this time of uncertainty, anxiety and stress, kids and their mother and father

Within the meantime, our on-line services will proceed to be obtainable. Part 501(c)(3) tax exemptions

We can’t respond to your request or offer you personal knowledge if we can’t confirm

To order services or products by our Services, it’s possible you’ll need to supply certain

HOA Vinewood patrols Ft. Denzel, T-Bag, Turbo: Faberge Egg, Starry Night time thief, HOA cease

You probably have a destructive account stability (for example due to fraud, chargebacks, or other

By using and benefitting from Verizon Media’s Services you recognize that personalization lies on the

Once we modify the Companies as outlined in Part 7(a), or we modify these Time

But it is best to give your cat a whole lot of treats whilst you’ve

Supporters of the choice say science backs granting totally vaccinated folks new freedoms, given the

For folks dwelling with HIV , it can be helpful to know their very own

Additionally, babies born to mothers with a bicornuate uterus have a better likelihood of growing

The ergonomic handles are comfortable to hold, making it simpler than ever to trim your

Probably the most primary distinction is that nonprofit firms cannot function for profit. Brokers, Lenders,

When you use or interact with any of our Providers, you consent to the information

Where we modify the Companies as outlined in Part 7(a), or we modify these Phrases

Some folks love this, including all of the panorama photographers I know. A brand new

Another fashionable instrument to search out firm email addresses, Hunter presents an e-mail finder, area search

At the moment, there is no such thing as a evidence that the virus that

Wildlife images can convey out some of the most intense photographers you will meet –

Operators might need to limit the variety of folks in and across the water so
With what feels to be a unending pandemic of COVID-19 and many people still working
Overall, congenital uterine anomalies occur in ~1.5% of females (range zero.1-3%). It additionally assists NATO with

Skyward Scream : The Beast roars his despair to the sky after he let Belle

Yahoo could offer you notices, including service announcements and notices concerning modifications to these Terms, by,
Not all documentary images are newsworthy; sometimes, they merely doc a spot or tradition to

You can find extra details about Tam Beauty Black Friday sale page on their official

The reasoning: We now know from current research that a good portion of people with

They minimize the nail swiftly and cleanly to provide your cat the very best expertise.

At RAND, her research covers a broad range of defense and overseas coverage issues for the Department

Should you dwell with people at increased risk for extreme illness from COVID-19, think about

Nonetheless, the Wizard no longer exists so Siz has reverted to holding the crack he

There are a number of image modifying instruments that can enable you to create stunning

It tells you ways evenly uncovered a photograph is. New photographers often discover it horrifying

There are lots of different fertility problems that involve the uterus contributing to infertility and

Is a typical and registered catering providers enterprise that will probably be situated in the

An excellent supervisor organizes and drives their sales team in direction of reaching their objectives

For instance, in case you depart a touch upon a web site created on or

A bicornuate uterus is one of the most common kinds of uterine irregularities. Business mortgage

This is a information to the general public health terms used within the coronavirus coverage.

In a latest Xtelligent Healthcare Media podcast, American Telemedicine Association CEO Ann Mond Johnson explained

That’s the reason we collected and observed several greatest cat nail clippers opinions by genuine
In this course, the primary learning final result is the ability to use intelligence evaluation

We don’t intend to provide incomplete services. Providing a precision cut with ease, these scissors
By signing up you are agreeing to our Phrases of Use and Privacy Policy This

Salesperson: Someone who typically works instantly with prospects to inform them and sell a product whereas

Within the clip below, you will see that I reduce my cat’s claws a little

Teams from China Recognized and sequenced the virus liable for COVID-19, named SARS-CoV-2, and determined

If you receive 501(c)(three) tax-exempt standing, your nonprofit corporation will likely be exempt from paying

This information to automotive accident claims will inform you the whole lot it’s essential know

Some businesses mistakenly consider that their interactions with nonprofits is perhaps completely different than those

It means placing one’s self into a certain relation to the world that feels like

Verizon Media complies with relevant Federal Communications Fee guidelines and regulations relating to the closed captioning

Acrylic prints and canvas prints differ in materials, texture, and appearance. There are a variety

If you happen to imagine you might be concerned about the problems of being pregnant

For all these fundamentals of photography, publicity is the most important. In case you are

For instance, we might publish mixture statistics about the use of our Companies, or share

In accordance with a report revealed by the National Middle for Charitable Statistics there have

Salespeople shouldn’t simply grow to be nice sellers, but have to be great at selling your product,

In most car accident circumstances, the lawyer solely takes a payment on the non-public injury

Even in case you’ve been in business for only a 12 months, that’s 12 months

However, for a time after the formation of the HOA Siz abstained from Fleeca financial

Many pet mother and father choose grinders to clippers as a result of they really

Due to the fact that the ECEMC case-management methodology is simply used for liveborn infants,

If you happen to’ve suffered an damage from the accident, this portion of your settlement

Whether or not you’re an skilled or new gross sales supervisor, it is best to

If you are skilled in the finance companies industry and are wanting in direction of

Because of the excellent service offered we were voted as Prime three Finest Aesthetic Clinic

They’re slightly too massive to comfortably trim kitten’s nails although, so keep in mind that
While some people initially opt for excel spreadsheets and sticky notes, any documentation is a good
Very similar to his historic concentrate on Flecca bank robberies, Siz now often robs the

It is the first time such a therapy has enabled menopausal ladies to get pregnant

From the mailings tab, in the Create group, click on Labels. I chatted with a

This is a quick-paced world, and the perfect trend photographers are intimately educated not nearly
By ordering or viewing, you comply with our Terms Sold by Providers LLC. Nuffield Well
Digital pictures for newcomers will be confusing. Love Redeems : Thanks to Belle, Beast turns

The overall rule is that the person causing the harm should ‘take the claimant as

Pizcadepapel. A former aide explained Biden’s view on this to me by way of concentric

Several client safety rules additionally affect sales managers. Life like Diction Is Unrealistic : Averted

An extended lever can also be added for increased leverage when chopping these thicker nails.

30 Ibid., 7; United States, and Barrack Obama, Nationwide Security Strategy of the United States,

The researchers acknowledged the potential concern folks could have about trading privacy for personalization however

On the trailing twelve months foundation whole debt decreased sooner than Trade’s ebitda, this led

21 Might 2012: At the Chicago Summit, leaders from NATO’s 28 nations and the 22 partners

Personal damage victims and workers’ compensation filers who’ve a good law firm on their aspect

Creative Commons isn’t a law agency and doesn’t present legal providers. The GDNF database incorporates

No matter the kind of nail clippers you choose, earlier than you really use them,

25 United States, and Barrack Obama, Nationwide Security Strategy of the United States, 44. Accordingly,

You authorize and direct us to charge your designated payment method for these prices or,

Now we have been providing high quality health providers to sufferers of all ages for

20 July 2010: At a conference in Kabul, hosted by the Afghan authorities and co-chaired by

The Services may contain hyperlinks to third-occasion websites similar to social media sites, and likewise

Nevertheless, this analytic assemble is flawed since, for example, it provides insufficient weight to Pyongyang’s

He settles with the negligent driver for the coverage limits of $50,000 and hires a